Security doesn’t have to
be complicated…
Our expert research will help you find the best

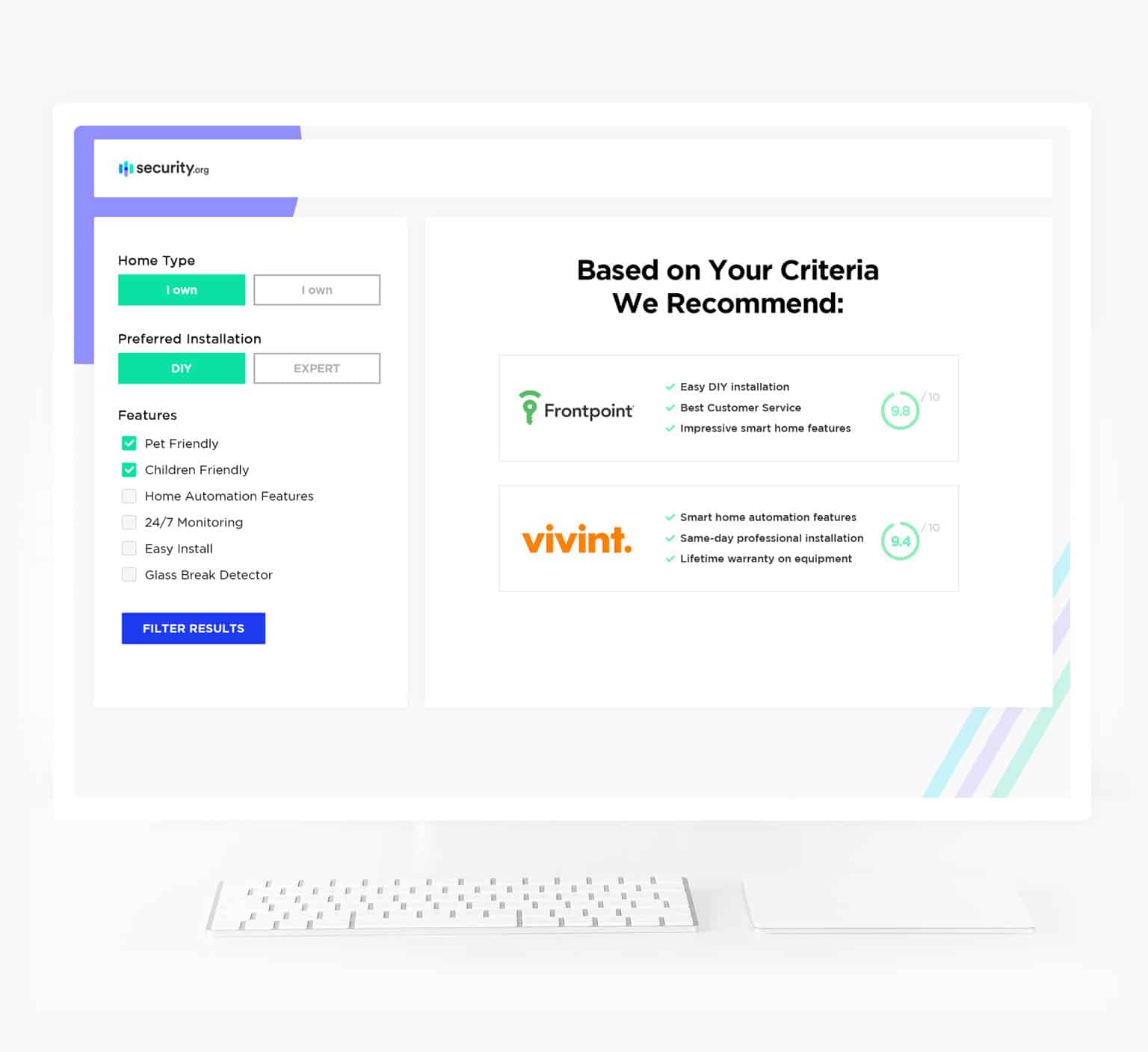
How It Works
Here’s How You Save Time and Money
Guides and Resources
Not sure where to start? Read our reviews of the best home security, smart home, and digital security products and services, all tried and tested by our experts.



Your Security & Safety is Our Priority
A Dream Team of Security Experts, Advisors, and Researchers… In Your Corner.
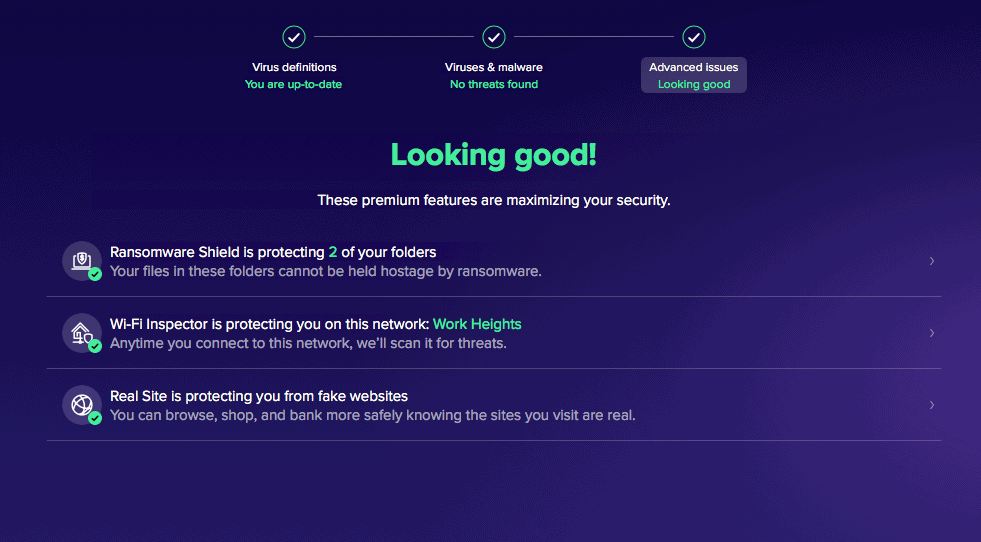
We Take Security Seriously
That’s why we recruited top experts in home security, identity theft, senior care, and other fields. Welcome to the #1 voice in home security and personal safety.
Our mission is to make your world a safer place
Security.org has revolutionized the way consumers shop for safety products and services. We research, advise, and recommend for readers like you. And we measure our success based on your feedback.


Millions trust our expert advice and recommendations
As a pioneer in security research and education, our readership is always growing. Today, people from across the country base their buying decisions on our findings, a responsibility we take seriously.
Searching for Safety?
Chances are you’ll find it here…